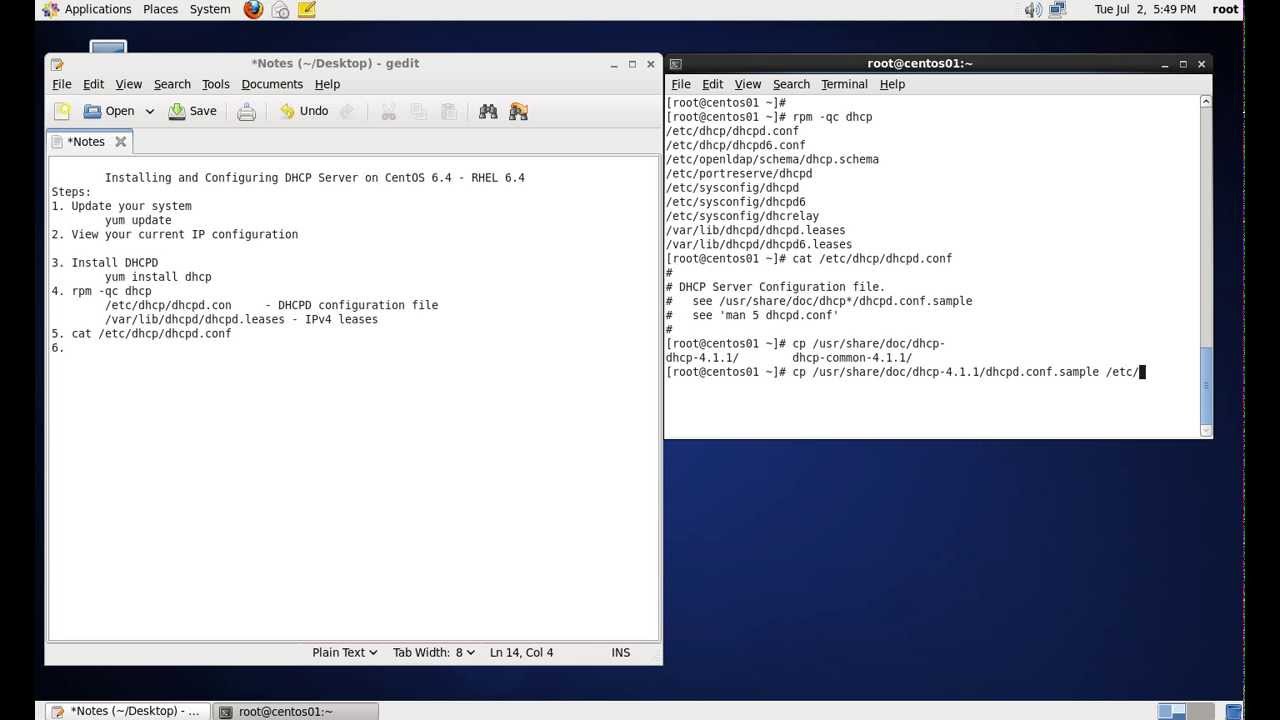
Install and Configure DHCP Server on CentOS 6.x – RHEL 6.x
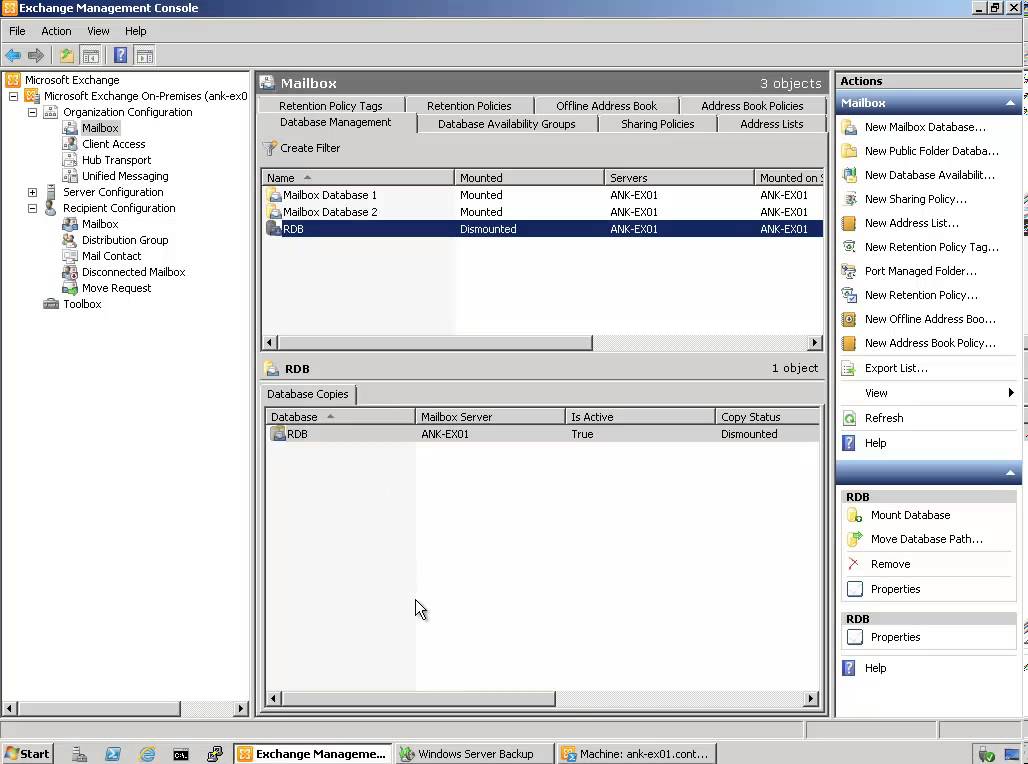
What is DHCP? DHCP stands for Dynamic Host Configuration Protocol. DHCP is a standardized network protocol used on Internet Protocol networks for dynamically distributing network configuration parameters, such as IP addresses for interfaces and services. DHCP is configured in a server-client model. DHCP server is the one assigning IP Addresses to client computers on the network. Each client is assigned a unique IP Address. DHCP server has a number of IP Addresses available in it’s pool. Steps: 1. Install DHCP yum install dhcp rpm -qc dhcp /etc/dhcp/ - container for DHCPD configuration /etc/dhcp/dhcpd.conf - IPv4 config /var/lib/dhcpd - container for leases /var/lib/dhcpd/dhcpd.leases - IPv4 leases 2. Enable DHCPD service chkconfig dhcpd on 3. View dhcpd.conf file cat /etc/dhcp/dhcpd.conf 4. Copy sample conf file to /etc/ cp /usr/share/doc/dhcp-4.1.1/dhcpd.conf.sample /etc/dhcp/dhcpd.conf 5. Edit the…